hermes goal 1.cmd | Working with the Command Line hermes goal 1.cmd This is how one can talk to hermes on the command line: websocat -t --insecure -H="X-Jwt: $(cat hermestoken)" --ws-c-uri=wss://signaling.vn.teslamotors.com:443/v1/mobile . Of course fans ran on the field at Super Bowl 58 between Chiefs and 49ers [VIDEO] Two partial streakers ran on the field during the third quarter of Super Bowl 58 Chiefs vs. 49ers. By Benjamin Zweiman and Nick .
0 · hermestarget.cmd/hermesgoal4.cmd
1 · hermes.exe Persistent start command
2 · Working with the Command Line
3 · What is Ryuk Ransomware? The Complete Breakdown
4 · Tesla Signaling/Hermes Protocol to send vehicle commands
5 · Malware Hermes folder? Anyone know what is it? : r/AcerNitro
6 · MISSION 2: HERMES RECONNAISSANCE
7 · How to try Static Hermes · facebook hermes · Discussion #1137
8 · Hermes Ransomware
9 · Hermes Ransom Help & Support Topic
So how does one spot a fake Louis Vuitton bag? Today, we’ll be talking all about how to tell if you have a real Louis Vuitton bag and some of the key ways you can spot a fake while shopping. Check out what's in this post! 10 Ways to Spot a Fake Louis Vuitton Bag. 1. Monogram. 2. Lining. 3. Stitching. 4. Heat Stamp. 5. Handles. 6. Zippers. 7.
Kaspersky teilte mir gerade mit, dass 2 Prozesse 'beschränkt' vertrauenswürdig sind. Diese sind hermestarget.cmd und hermesgoal1.cmd. Was ich nun direkt komisch fand .

My computer is Acer Nitro 5 with Windows 11. Other files named "Hermes" could be found in folder Acer Jumpstart - "Hermes.exe", and in Microsoft OneDrive folder, named "Hermes.dll". . This is how one can talk to hermes on the command line: websocat -t --insecure -H="X-Jwt: $(cat hermestoken)" --ws-c-uri=wss://signaling.vn.teslamotors.com:443/v1/mobile .
Hermes is commodity ransomware that has been observed for sale on forums and used by multiple threat actors. However, Ryuk is only used by WIZARD SPIDER and, unlike .
If it was identified by filemarker or extension, then it is the Hermes 2.1. It's possible they just slightly modified the ransom note. Hermes 2.1 is not decryptable just like ID . Are there binaries distributed to try out Static Hermes or should you build it by yourself from the branch? I might have accidentally installed a ransomware-laden software called 'Jcleaner" from Vitsoft. MB3 was able to detect and quarantine/delete it. However, there seems to still be .
The shell (or "command line") allows you to interact with Athena without using the mouse. Most tasks on Athena can be accomplished either by using the mouse and the .MISSION 2: HERMES RECONNAISSANCE. Welcome, Cadet, to the HERMES Software Suite. Your mission is to gain control of this unruly collection of files and programs. To do that, you need to know the lay of the land. Your reconnaissance training will help you to answer these questions: What programs are available and what do they do? Kaspersky teilte mir gerade mit, dass 2 Prozesse 'beschränkt' vertrauenswürdig sind. Diese sind hermestarget.cmd und hermesgoal1.cmd. Was ich nun direkt komisch fand war, dass sich unter den vertrauenswürdigen Prozessen/Programmen noch 3 Programme mit ähnlichem Namen finden ließen: hermesgoal2.cmd, hermesgoal3.cmd und hermesgoal4.cmd .
My computer is Acer Nitro 5 with Windows 11. Other files named "Hermes" could be found in folder Acer Jumpstart - "Hermes.exe", and in Microsoft OneDrive folder, named "Hermes.dll". Do anyone know what is that OEM folder, and if I should be concerned? This is how one can talk to hermes on the command line: websocat -t --insecure -H="X-Jwt: $(cat hermestoken)" --ws-c-uri=wss://signaling.vn.teslamotors.com:443/v1/mobile ws-c:log:ssl:tcp:signaling.vn.teslamotors.com:443 - [WARN websocat::ssl_peer] Connected to TLS without proper verification of certificate. If it was identified by filemarker or extension, then it is the Hermes 2.1. It's possible they just slightly modified the ransom note. Hermes 2.1 is not decryptable just like ID Ransomware. What is HERMES virus? STEP 1. Reporting ransomware to authorities. STEP 2. Isolating the infected device. STEP 3. Identifying the ransomware infection. STEP 4. Searching for ransomware decryption tools. STEP 5. Restoring files with data recovery tools. STEP 6. Creating data backups. Reporting ransomware to authorities:
Hermes is commodity ransomware that has been observed for sale on forums and used by multiple threat actors. However, Ryuk is only used by WIZARD SPIDER and, unlike Hermes, Ryuk has only been used to target enterprise environments. Are there binaries distributed to try out Static Hermes or should you build it by yourself from the branch?
hermestarget.cmd/hermesgoal4.cmd
I might have accidentally installed a ransomware-laden software called 'Jcleaner" from Vitsoft. MB3 was able to detect and quarantine/delete it. However, there seems to still be a persistent start command for it (as seen in the screenshot). I have. The shell (or "command line") allows you to interact with Athena without using the mouse. Most tasks on Athena can be accomplished either by using the mouse and the graphical environment, or by using the shell, but some advanced tasks require shell commands. I've taken some feedback and updated the terminals. Biggest thing to note is, these are based off the warhound terminal, 2 of the 3 titan loadouts have "paired" weapons, which in this case just means the card is doubled up to take 2 slots. Kaspersky teilte mir gerade mit, dass 2 Prozesse 'beschränkt' vertrauenswürdig sind. Diese sind hermestarget.cmd und hermesgoal1.cmd. Was ich nun direkt komisch fand war, dass sich unter den vertrauenswürdigen Prozessen/Programmen noch 3 Programme mit ähnlichem Namen finden ließen: hermesgoal2.cmd, hermesgoal3.cmd und hermesgoal4.cmd .
ysl panty
My computer is Acer Nitro 5 with Windows 11. Other files named "Hermes" could be found in folder Acer Jumpstart - "Hermes.exe", and in Microsoft OneDrive folder, named "Hermes.dll". Do anyone know what is that OEM folder, and if I should be concerned? This is how one can talk to hermes on the command line: websocat -t --insecure -H="X-Jwt: $(cat hermestoken)" --ws-c-uri=wss://signaling.vn.teslamotors.com:443/v1/mobile ws-c:log:ssl:tcp:signaling.vn.teslamotors.com:443 - [WARN websocat::ssl_peer] Connected to TLS without proper verification of certificate.
If it was identified by filemarker or extension, then it is the Hermes 2.1. It's possible they just slightly modified the ransom note. Hermes 2.1 is not decryptable just like ID Ransomware.
ysl nude lingerie lipstick
hermes.exe Persistent start command
What is HERMES virus? STEP 1. Reporting ransomware to authorities. STEP 2. Isolating the infected device. STEP 3. Identifying the ransomware infection. STEP 4. Searching for ransomware decryption tools. STEP 5. Restoring files with data recovery tools. STEP 6. Creating data backups. Reporting ransomware to authorities: Hermes is commodity ransomware that has been observed for sale on forums and used by multiple threat actors. However, Ryuk is only used by WIZARD SPIDER and, unlike Hermes, Ryuk has only been used to target enterprise environments. Are there binaries distributed to try out Static Hermes or should you build it by yourself from the branch?

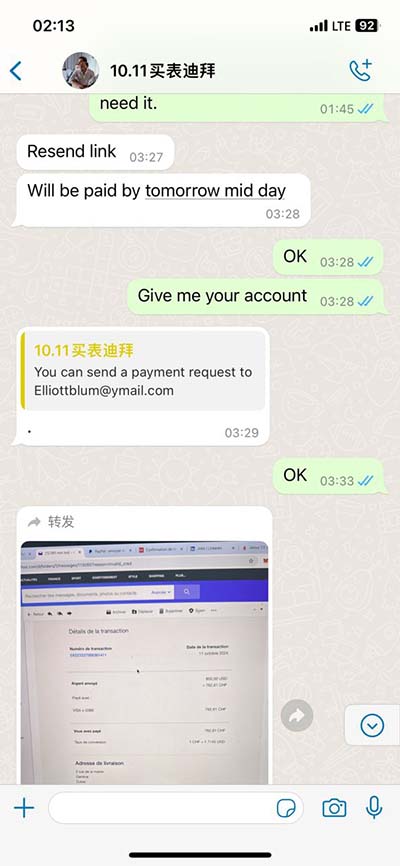
I might have accidentally installed a ransomware-laden software called 'Jcleaner" from Vitsoft. MB3 was able to detect and quarantine/delete it. However, there seems to still be a persistent start command for it (as seen in the screenshot). I have.
The shell (or "command line") allows you to interact with Athena without using the mouse. Most tasks on Athena can be accomplished either by using the mouse and the graphical environment, or by using the shell, but some advanced tasks require shell commands.
Working with the Command Line

Louis Vuitton nanogram ring size M | Pink Gold and Silver LV ring | Monogram LV. (88) £89.59. FREE UK delivery. Vintage Fendi Gold & Crystal Ring Boxed. (28) £90.00. Louis Vuitton Authentic Vintage Key Holder. (3) £43.58. Rare Vintage Louis Vuitton LV Checked Monogram Key Wallet-86. (24) £69.00.
hermes goal 1.cmd|Working with the Command Line